With the amount of time that we spend interacting with computers rising every day, and seemingly continuing to do so all the time, being safe and secure while online is a very important thing for everyone. We know that there are hackers and malicious programs out there that can compromise our systems if we don't take security seriously, but with the ever-increasing variety of attacks on our digital lives, we must look at the bare minimums required to staying safe on your computer.
While there are new threats coming out every day, the best way to stay as safe as you can is by ensuring your system is secure at the most basic levels. This is why we have put together a guide that will go over the best practices for staying safe while online, what to watch out for, and many other aspects of securing your system and staying safe online.
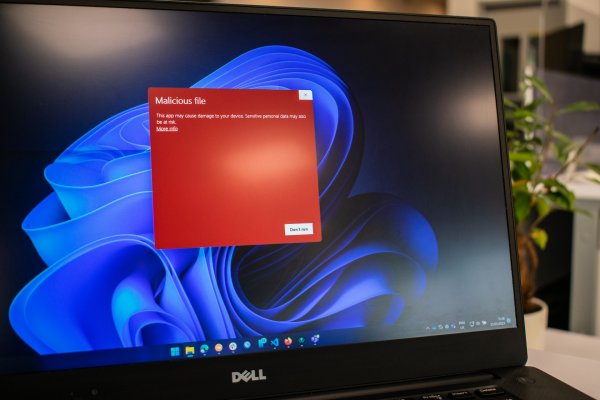
Malware and computer viruses are a major threat to the security of your computer. It is important that you understand what these malicious programs are, what types exist, and how to protect yourself from them. Malware is short for malicious software, which refers to any form of a program or code with the intent of damaging or disrupting systems. Computer viruses are one type of malware that can be spread through emails, downloads, or other sources and can cause damage ranging from minor annoyances to system crashes or data loss.
Other common types of malware include spyware, ransomware, worms, Trojan horses, and adware. Spyware is designed to collect information without permission, while ransomware locks files until money is paid to release your files back to you. Worms are self-replicating pieces of malicious code that propagate themselves throughout a network, while Trojan horses disguise themselves as useful programs but install harmful content on a user’s machine. Adware is also known as unwanted applications that deliver targeted advertisements when installed on a device.

To protect against these threats, it is essential to keep your antivirus software updated and scan regularly for suspicious activity. Additionally, take precautions when downloading new files, such as only using secure websites and avoiding questionable links sent via email or text message. Being aware of potential risks will help ensure your computer remains safe from malicious attacks.
And now that we have a basic understanding of the common types of malicious programs that might impact your computers safety, we are going to move on to the first step in our security guide; which is making a backup plan.
Creating a backup system is essential to safeguarding your data against disaster. There are various strategies you can use to create backups, such as using cloud storage or external hard drives. Cloud storage offers the capability of backing up data in real-time and allows for multiple copies of files to be stored offsite. External hard drives provide quick access to large amounts of data and allow for local recovery if needed. We have done some good reviews about the best online backup options on our site, so if you do not currently have a cloud option make sure you check out our reviews.
If possible we suggest a combo of a cloud-based backup as well as a physical backup hard drive that is separate from your computer. By utilizing both traditional and modern methods, users can stay safe from potential threats while ensuring their critical information remains protected at all times.
Now that we have your data backed up, we will take the first step in preventing any infections and that is by installing security programs on your computer.
With all of your most important files in a safe and secure place it is time to start building your defense against malicious programs, and this is done by installing antivirus or antimalware programs onto your system. It is important to install security software on your computer in order to avoid malware and viruses from getting in, as well as identifying them and remove them if they do make their way onto your hard drive.

It’s important to select the correct security software for your needs, as there are numerous options available so if you are unsure of where to start, make sure you check out our top-rated antivirus reviews. After installation, it is crucial to maintain the security software regularly in order to ensure maximum protection of your computer system. This includes updating the software when necessary and ensuring scans are performed frequently.
Now we will move onto the next step of fortifying your computer against infections, and that is to plug up any possible vulnerabilities in your operating system and program files.
While it might not sound exciting, the most important thing to do is to stay current with your operating systems updates. Operating systems come with built-in security features that help keep malicious software and hackers out, and regular updates contain new patches that improve these defenses. Additionally, updating other software on your device, such as drivers or Adobe Flash, will ensure it's secure against exploits. To stay informed about available updates, turn on update notifications in your settings menu so you don’t miss any critical ones.
In most cases, your operating system will prompt you if you would like to update your code, so it shouldn't be that much extra work. Some specific programs require you to check for updates, but if there is a large security flaw found you will usually get some type of notification that an update is required.
Firewalls are an essential tool for keeping your network secure. Firewall protection helps ward off potential attacks on the network and can also be used to monitor incoming traffic, blocking malicious content while allowing legitimate connections to pass through. Network firewalls provide an important layer of security against external threats by preventing unauthorized access from outside sources. By using a firewall, you can prevent attackers from gaining access to sensitive data or exploiting vulnerabilities in your system.
When setting up a firewall, it is important to configure the settings correctly so that only authorized users have access to your resources. You should also regularly update your firewall software with any new patches or bug fixes as they become available. Additionally, make sure that you keep up-to-date antivirus software installed on all computers connected to the network in order to protect against any malware threats. Implementing these measures will help ensure that your network remains safe and secure at all times and that no one gains unauthorized access.
While we will admit that this is a bit of a more advanced security feature there are a lot of videos online that can guide you through the setup process. It is important to note that if you don't setup your firewall correctly it might look like you are having internet issues, as it can prevent connections.
Wi-Fi networks are vulnerable to attack without secure passwords in place. It’s very important to use strong passwords for your network, as weak passwords will leave you exposed and open to malicious actors. With the right password protection, you can ensure that your Wi-Fi is secure from external threats. To create a strong password, make sure it’s at least 12 characters long and contains upper- and lower-case letters, numbers, and symbols.

While it might be easier to use a familiar password, your family's last name, or other easy to remember codes the goal is to prevent people from guessing so the stronger the password the better the protection. It might not be fun taking out that note that keeps the password on it, but it improves your security and we would suggest doing it this way.
Now that you have secured your Wi-Fi network with a strong password, it is important to educate yourself about online threats. Cybersecurity knowledge is the first step in protecting yourself from cybercrime. The more aware you are of potential risks and dangers on the internet, the better prepared you will be in preventing them. And while we understand that reading about infections isn't exciting, there have been times in the world when prevention and knowledge could have stopped huge infections like the Conficker virus which infected Millions of systems worldwide.
If people had been a bit more vigilant about security there is a chance that the damage from this infection could have been reduced, instead of the millions of dollars, it cost computer users all over the world.
It is important to avoid suspicious links and downloads when browsing the web and in your email. Many infections can pose themselves as legitimately named files, like Adobe or Chrome, but in reality are viral infections. On top of this they can also look like email attachments that you would want to see. A general email saying look at these pictures I found of these cute dogs might sound great, but it could actually be a virus in disguise!
Malicious software can be embedded in some of these links, so it’s important to identify which ones are malicious. When clicking on a link, pay attention to where it takes you. If it seems like an unfamiliar website or if there are many pop-up ads, do not click any further. Additionally, try hovering your mouse over the link before you click; this will show you the URL that the link leads to.
Be sure to also check out the source of a download before completing it—make sure you trust who created the file and its contents.

Now that you know how to recognize legitimate email attachments and links, it’s important to make sure your computer is kept up-to-date. Installing third-party updates for apps and plugins is a key element of keeping your device secure. Security updates can patch potential vulnerabilities in software applications that can be exploited by hackers, so they should always be installed as soon as possible after release. App and plugin updates may also add new features and bug fixes, allowing them to work more efficiently on your device.
Like we reviewed above with the operating systems updates and patches, many times programs will push out updates if security holes are found. So if you get a notification we suggest that you do the update, and not just push the remind me later button. Delaying an update could allow malicious programs to get in through the older versions' vulnerabilities.
Now that you have a better understanding of data protection rules, it’s time to take the next step and configure your privacy settings on social media platforms. All major social media sites offer users the ability to adjust their privacy settings in order to protect personal information and control who can access certain posts or profile details.
To start off you should read through the terms of service for each platform before setting up an account. This will give you an idea of what kind of data is collected and how it may be used by third parties. Once you are familiar with these policies, make sure to configure your privacy settings accordingly across all accounts.
While each person has their own level of privacy online, we suggest that you don't have an open profile. Many times hackers will find data on you via your profile, like your pets name, and use them to try to hack into your other accounts. This again goes back to the value of a hard to guess password like we spoke about earlier in our article.
Using a virtual private network, or VPN, is an effective way to protect yourself online. A VPN creates a private network within the public internet by using encryption technology. This ensures that all of your data and activity remain secure while you are connected to any website or application. With this extra layer of security in place, you can browse without worrying about hackers trying to access your information.
This will not only encrypt your data transfer for the protection of the data being moved but can also prevent people from tracking your data transfer, so it isn't only about security but adding a level of privacy to your online activities.
While we know that we have just scratched the surface of internet security we hope that our guide has been able to, at the very bare minimum, raise the idea of how important your security should be taken while you are online. Every day there are thousands of new infections coming out that all are trying to get into your system for one reason or another.
We are not trying to create a feeling of paranoia, but just like in real life, you should be aware of your actions and environments while online. You never know what files you might be downloading, or what might happen if you go to a site by mistake and get some malware on your system.
By setting up a good basic security protocol you will be able to protect yourself against a large majority of malware and other malicious programs from getting on your system. And by paying attention to the files and sites you interact with you will add another layer to your security. Couple this with the use of strong passwords, and other safety tips we outlined in this article and you shouldn’t have much to worry about while you are online.
If you have made it this far and want more information, here is a great video that can go over more tips ( and some tips we had) in a bit more detail: